TRUSTED BY
Get Real Security Insights for Your Business
Identify vulnerabilities before hackers do with advanced penetration testing. Strengthen your system’s defenses against cyber threats and unauthorized access.
Our Achievements
Recognized as "Top ArtificiaI Intelligence Company" by Clutch.
Job Success Score 100%
Consistent Quality. Zero Compromises.
Rewarded "Top Mobile App Development Agency" by GoodFirms
Awarded "Top Software Development Companies in Chicago"
Penetration Testing Projects We Delivered Successfully
Since our inception, we have been serving customers with a holistic approach and a proven penetration testing strategy. We have grabbed opportunities to work on multiple projects and delivered them successfully as promised.
- Property Inspection
- Stop JEU
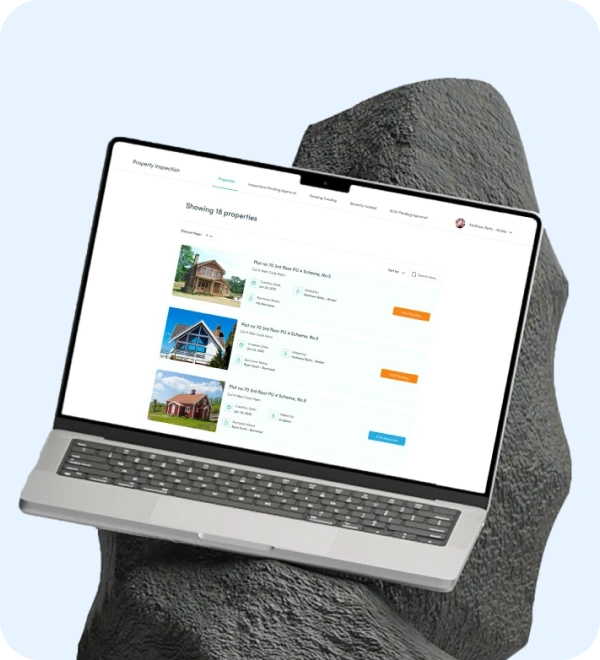
Property Inspection
The property inspection platform allows for expert inspections, smooth transactions, and a network you can trust. You can make informed real estate property-related decisions with the help of this platform. Moreover, it ensures a smooth buying/selling process with comprehensive inspections.
Category
- Real-Estate
Tech Stack
- Angular
- Node Js
- Java
- Swift
- PostgreSQL
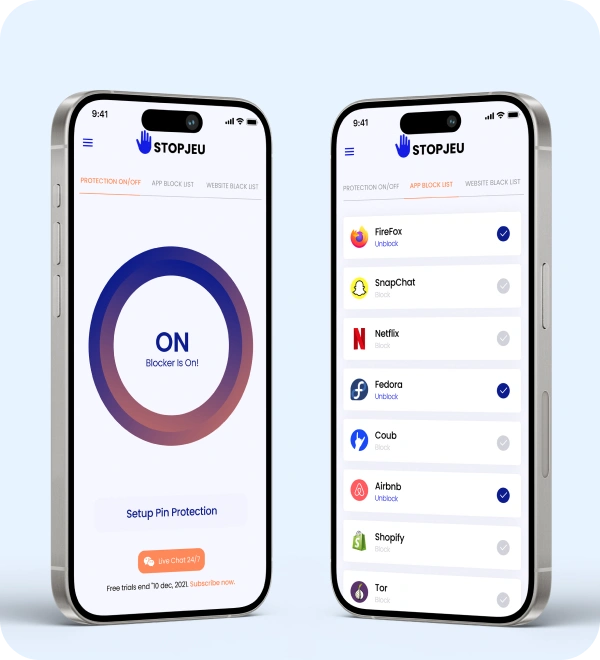
Stop JEU
Stop JEU is a robust VPN (Virtual Private Network) application designed to enhance users' online privacy and security. It has a range of customized features to protect users' digital footprints and ensure a safe online experience. Users can turn VPN protection on or off using the toggle option to control their online privacy instantly.
Category
- VPN and DNS
Tech Stack
- Android
- MacOS
- Windows
Client Experiences
Proactive Penetration Testing for Maximum Security
Detect and fix security weaknesses with simulated cyberattacks. Ensure compliance, protect sensitive data, and safeguard your digital infrastructure.
Penetration Testing Process
We use a systematic approach to conduct thorough penetration testing. Our approach to testing is based on several factors, including quality, innovation, and client satisfaction. We carry out the entire process in phases to ensure it runs smoothly and is completed on time.

1. Planning
- Define scope & objectives.
- Agree to the Rules of Engagement.
- Assign roles & escalation contacts.
- Produce signed deliverables like the scope doc, RoE, asset inventory, and rollback plan.
2. Reconnaissance
- Passive OSINT (DNS/WHOIS, cert transparency, public repos).
- Active discovery (port/service sweeps, banner/version fingerprinting).
- Enumeration (subdomains, endpoints, users/config metadata where allowed).
- Prioritize targets by exposure + business impact.
3. Vulnerability Assessment / Scanning
- Run automated scans (network, web/API, cloud, containers).
- Perform credentialed scans and config checks where permitted.
- Manually validate high/critical findings to remove false positives.
- Produce a prioritized vulnerability list with exploitability and remediation priority.
4. Penetration Testing
- Execute targeted exploitation on prioritized, in-scope findings.
- Chain exploits for privilege escalation / lateral movement (controlled).
- Capture non-destructive PoC evidence and test defender detection (SIEM/EDR).
- Clean up all artifacts and document persistence/removal steps.
5. Reporting
- Executive summary with top business risks and remediation roadmap.
- Technical findings with evidence, reproduction, and step-by-step fixes.
- Detection & monitoring recommendations (SIEM rules, logs to add).
- Retest / validation plan + Jira - ready remediation tickets.
Tools and Frameworks We Leverage for Penetration Testing
Why Choose Moon Technolabs for Penetration Testing Services?
As a leading provider of penetration testing services, we offer a thorough, customized security assessment tailored to your business’s specific needs. We provide comprehensive, detailed reports with actionable insights to help you strengthen your security posture. Our commitment to compliance, confidentiality, and proactive risk mitigation ensures your systems are fortified against evolving threats, giving you confidence in your organization’s security.
- Certified ethical hackers
- Customized testing approach
- Ongoing security support
Strengthen your Cyber Defense with Our Pen Testing
We help you identify vulnerabilities before hackers can exploit them, ensuring the full security of your business through specialized penetration testing.
Looking for other App Development Services?
FAQs
01
What do you require to proceed with any new penetration testing projects?
02
Will you resolve the already found vulnerabilities?
03
How much time do you take for penetration testing?
04
Do you sign an NDA?
05
How can penetration testing help protect my business?
06
Will penetration testing disrupt my business operations?
07