TRUSTED BY
Strengthen Your Security, Minimize Risks
Identify vulnerabilities and fortify your applications with our in-depth software security testing services. Ensure compliance, prevent cyber threats, and safeguard sensitive data.
Our Achievements
Recognized as "Top ArtificiaI Intelligence Company" by Clutch.
Job Success Score 100%
Consistent Quality. Zero Compromises.
Rewarded "Top Mobile App Development Agency" by GoodFirms
Awarded "Top Software Development Companies in Chicago"
Security Testing Projects We Delivered Successfully
We have successfully helped businesses across various industries secure their IT infrastructure, applications, and digital assets. Our case studies showcase our expertise and approach to delivering comprehensive security testing services.
- Property Inspection
- Stop JEU
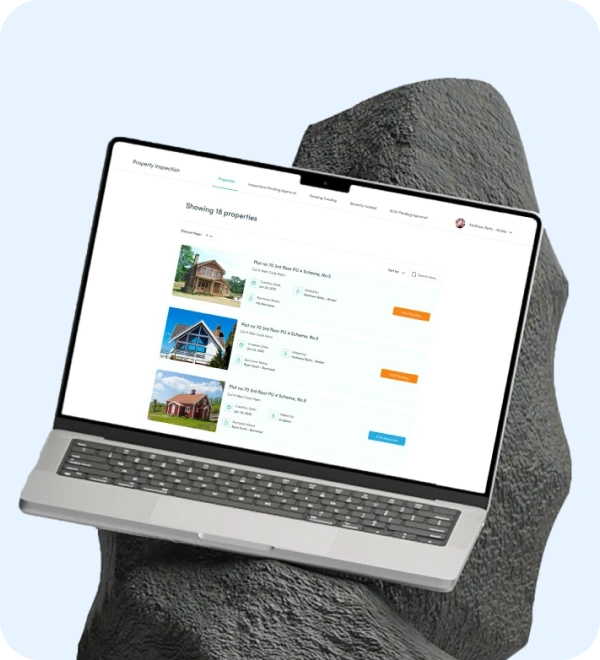
Property Inspection
The property inspection platform allows for expert inspections, smooth transactions, and a network you can trust. You can make informed real estate property-related decisions with the help of this platform. Moreover, it ensures a smooth buying/selling process with comprehensive inspections.
Category
- Real-Estate
Tech Stack
- Angular
- Node Js
- Java
- Swift
- PostgreSQL
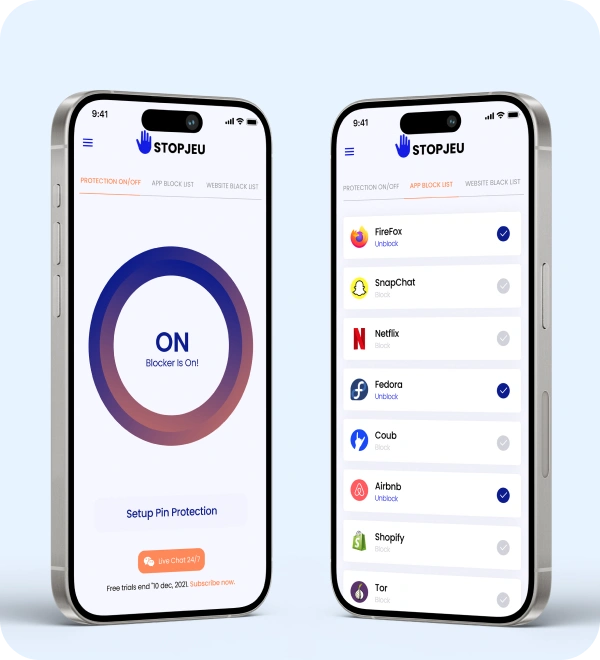
Stop JEU
Stop JEU is a robust VPN (Virtual Private Network) application designed to enhance users' online privacy and security. It has a range of customized features to protect users' digital footprints and ensure a safe online experience. Users can turn VPN protection on or off using the toggle option to control their online privacy instantly.
Category
- VPN and DNS
Tech Stack
- Android
- MacOS
- Windows
Client Experiences
Comprehensive Security Testing for Maximum Protection
Detect security gaps, prevent data breaches, and enhance system resilience with rigorous vulnerability assessments and penetration testing. Stay ahead of cyber threats.
Our Security Testing Process
We follow a structured approach to security testing, managing each phase efficiently and ensuring timely delivery. From requirement gathering to final reporting, our proven strategy ensures thorough analysis and precise results.

1. Requirement Gathering
- Understand project scope and system architecture.
- Identify security objectives and compliance needs.
- Define testing boundaries and authorized access levels.
- Gather relevant documentation (network diagrams, app flow, API details).
2. Information Gathering
- Perform passive reconnaissance and OSINT.
- Enumerate subdomains and review public code repositories for exposed secrets.
- Map exposed assets: domains, IP ranges, cloud services, and third-party integrations.
- Identify entry points and collect technology details to prioritize likely weaknesses.
3. Vulnerability Assessment & Scanning
- Conduct reconnaissance to gather system information.
- Perform network and application-level vulnerability scans.
- Identify known vulnerabilities, weak configurations, and exposure points.
- Analyze results to prioritize potential risk areas.
4. Exploitation & Post Exploitation
- Attempt to exploit identified vulnerabilities ethically.
- Validate real-world impact through controlled attack simulations.
- Escalate privileges, access sensitive data, or pivot within systems (if in scope).
- Document each exploit path and determine potential damage.
5. Reporting
- Compile a detailed report of findings with CVSS severity ratings.
- Include exploited vulnerabilities, their impact, and steps to reproduce them.
- Provide an executive summary for management and technical remediation guidance for engineers.
Tools and Frameworks We Use for Security Testing Services
Why Choose Moon Technolabs for Security Testing Services?
As a leading IT security testing company, we offer a wide range of services, including penetration testing, vulnerability assessments, and compliance checks, to fortify your systems against potential threats. Using cutting-edge tools and industry-best practices, we proactively identify and mitigate security risks, ensuring robust protection against evolving cyber threats. Our thorough testing, continuous support, and detailed reporting ensure your digital infrastructure remains secure, compliant, and resilient in a rapidly changing landscape.
- Customized security testing solutions
- Proactive threat detection
- Experienced security professionals
- Continuous monitoring and support
Proactive Security Testing for a Resilient System
Ensure end-to-end security with advanced testing strategies that detect, analyze, and mitigate risks. Protect your infrastructure and maintain data integrity.
Looking for other App Development Services?
FAQs
01
Can you test IoT solutions or devices?
02
What type of security solutions do you provide?
03
How much do you charge for providing security services solutions?
04
How can security testing help protect my business from cyber threats?
05
We handle sensitive customer data. How do you ensure our application remains secure?
06
Is security testing necessary if we already have a firewall and antivirus?
07
How do I know which type of security testing is right for my business?
08
Do you perform security testing on live production systems?
09
Can you integrate with DevSecOps pipelines?
10